Using Managed Identity in Logic Apps for Calling Active Directory Secured Function App
Introduction
In last posts we explored as to how AD authentication works -Understanding Azure Active Directory Authentication and Authorization using Oauth
With couple of examples on how to use it - Securing Function App with Azure Active Directory authentication and Calling Active Directory Secured Function App from Logic Apps
But there was couple of challenges - creation and management of the AD app, it's credentials and credentials getting exposed/becoming part of the code.
So we explored a better approach to call AD secured service using Managed Identity - Understanding Managed Identity and using it to Call Secured function App
In this post we will see how to use Managed Identity in Logic Apps for Calling Active Directory Secured Function App.
How to do it
1. Create Target Function app
Here we are going to call the same function app created in following post - Securing Function App with Azure Active Directory authentication
for that we would grab its url and AudienceID (client ID of AD app created to secure function App)
Create Logic App instance and click on Identity and then switch on the Status. That's it, an identity for your logic app is created - behind the scene, an AD app gets created in AD with the same name as that of the logic app .
So whenever this logic app has to call any AD secured Azure service, the above created Identity would be leveraged.
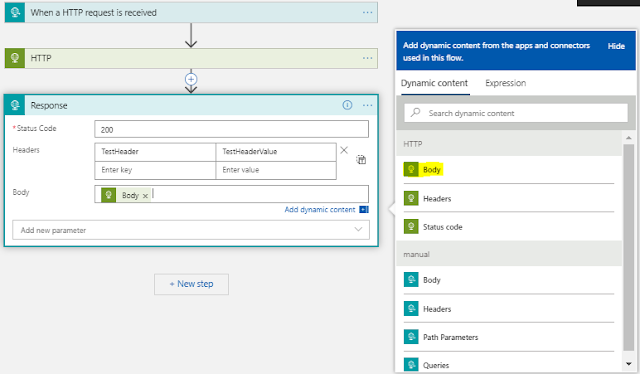
Create a simple http triggered logic app which will get triggered upon receiving http request and then calls the secured function app and sends back response . In response it will add whatever received from secured function app.
In second step note that we are using HTTP action rather than using Azure Functions action and it is because Azure Functions action does not support adding authentication details, whereas Http connector is flexible with it.
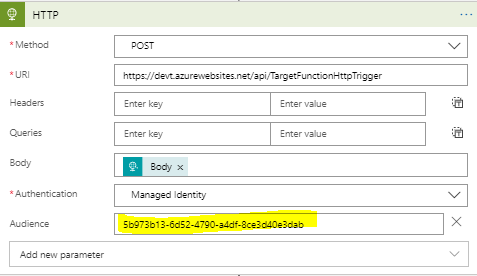
After adding http action, Select POST as method and provide the url of secured function app. In Authentication select Managed Identity and Click on Add new parameter
And provide the Audience ID we grabbed in step 1 as shown below
Now add http response action and against body - select the body returned from above step
That's it logic app is ready to use.
Testing
The target function expects input in following form
{"name":"Input"}
and it returns result as "Reply from target app,+input it received"
How it works
If you noted, we haven't provided any credentials of Logic app and just provided the url of the function to call and Audience ID and still Logic app was able to get response back -- it is because under the hood logic app runtime uses the Identity created in step 2 to authenticate itself with Active directory and gets the access token to make a call.
Thus with help of Managed Identity, overhead of managing AD app and credentials is removed.
Thus with help of Managed Identity, overhead of managing AD app and credentials is removed.
Related Post
- Understanding Azure Active Directory Authentication and Authorization using Oauth
- Securing Function App with Azure Active Directory authentication
- Getting Started with Logic Apps - Enterprise Application Integration
- Getting Started with Logic Apps - EDI X12 Fundamentals
- Getting Started with Logic Apps - Fundamentals
- Getting Started with Logic Apps - AS2
- Getting Started with Logic Apps - XML to EDI X12











Comments
Post a Comment